National Cyber Security Awareness Week | Do you understand the professional “cyber talk” used in cyber cases?
IP address
Internet Protocol Address
domain name
Domain Name
DNS
Domain Name System
.png)
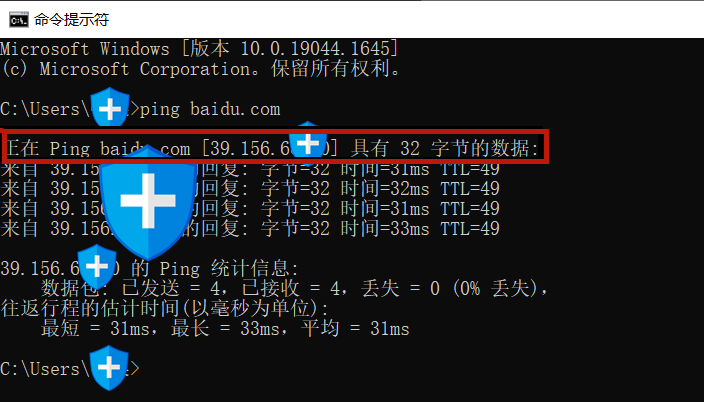
domain name server
Domain Name Server, DNS
Traffic hijacking
Traffic Hijacking
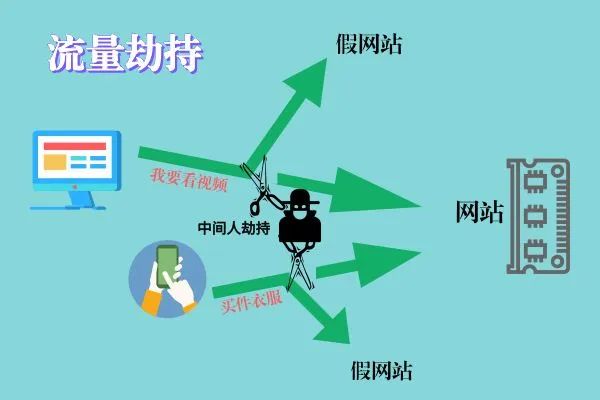
DNS hijacking
Domain name hijacking
DoS attack
Denial of Service
DDoS attack
Distributed Denial of Service

broiler chicken
"Meat machine" "Puppet machine"
Internet of things
IoT, Internet of things

Warmth hint
Today's class is a bit difficult. Did you learn anything?
Be sure to remember: Never use network technology Commit illegal crimes, otherwise the Internet police aunt will follow the Internet cable and come to you...





 中文简体
中文简体 英语
英语










 Chengnan Development Zone, Diaobingshan City, Liaoning Province, China
Chengnan Development Zone, Diaobingshan City, Liaoning Province, China +86-13130789295
+86-13130789295 +86-024-76755566
+86-024-76755566 +86-024-76755566
+86-024-76755566 lnwyjt@lnwyjt.com
lnwyjt@lnwyjt.com